 Every year, bang on April 1st, there is a huge surge in phishing attacks across all media. Cyber criminals try in even greater numbers, with tricks and apparent April Fool’s Day jokes, to steal personal information and login details from unsuspecting users and, ultimately, to steal their money Not only phishing emails make the rounds on April 1st- and all other days of the year. Care is also called for in social networks and when using messenger software.
Every year, bang on April 1st, there is a huge surge in phishing attacks across all media. Cyber criminals try in even greater numbers, with tricks and apparent April Fool’s Day jokes, to steal personal information and login details from unsuspecting users and, ultimately, to steal their money Not only phishing emails make the rounds on April 1st- and all other days of the year. Care is also called for in social networks and when using messenger software.
Unsuspecting users are often duped by videos and messages. The scammer know exactly how quickly so-called “shocking video material” is spread through social networks and counts on the curiosity of the online community. Caution must be exercised not only with message on social networks, but also with e-mails in personal inboxes. In the past, spam emails, for example, were easily recognised by obvious spelling mistakes and poor writing style. However, spam today can take the form of emails from all kinds of companies in perfect corporate design. Sometimes the recipient is even addressed by name and convincing, but fake, customer or tracking numbers are included in the message body.
What to watch for: Often various links are included in the text which appear to be linked to the fake website of the supposed company, e.g. a bank. On the fake website you are usually asked to provide personal information and requested to enter your login details into a form. Your computer could also be infected with a virus by “drive by download” on such pages. An email could have an attachment that purports to have further information. Do check, is the attachment really what it claims to be?
How to recognise phishing emails:
• Email addresses, e.g. PayPal, Amazon, DHL, can be very convincingly fake and hard to distinguish from the real thing. Checking the email header and IP address can be very informative.
• Grammar and spelling mistakes. The whole email could even be in a different language.
• Phishing message are often not personalised. The salutation, so “Dear Sir” or “Dear Madam”, could be wrong and apparent customer numbers are bogus.
• Criminals use emotional language in their phishing emails or try scare recipients into doing something.
• Phishing emails often include suspicious links or attachments.
• The website linked to in phishing messages can be quite similar to the real legitimate website.
• Pay attention to the security certificate of the webpage you have been forwarded to. Is the lock next to the address shown in the browser closed and green?
• Users are often asked to enter personal details and even their login details.
Never download software from such questionable websites! NEVER open the suspicious attachments of spam or phishing emails!
Examples of personal information asked for on phishing sites:
• User names and passwords
• Social security numbers
• Bank account details
• PINs
• Complete credit card details
• Mother’s maiden name
• Your birthday or date of birth
How you can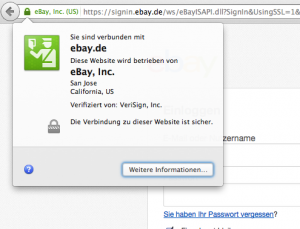 tell whether the website of the company is legitimate or not:
tell whether the website of the company is legitimate or not:
Whenever you are asked to identify yourself or when you are buying things online of using internet banking, make sure that the browser is using the encrypted connection HTTPS (see image). Ideally, you should also check the site certificate and make sure it is legitimate. Find more about how to recognise a safe connection in your browser: “How to know if an online transaction is secure”.
 The email has an attachment. Is it real or not?
The email has an attachment. Is it real or not?
Criminals use various tricks try to make attachments look like harmless documents, or they pack the malware into several layers of archives (zip) to e.g. get past security software. If the email is not one you are expecting, then you should NEVER think of opening the attachment just for fun. Opening the attachment activates the malware and installs it on your computer. All kinds of scenarios are possible, even to the point of your computer being taken over completely by criminals.
If you really are not sure, then save the attachment (never open it) and upload it for free to virustotal.com to be checked. Over fifty anti-virus programs will scan the file for infections and you can be totally sure whether it is clean or not. Delete the file immediately, should it be infected.
Tips from the Botfrei team
It is not only emails you need to be careful with. Apparent messages from friends can have been sent from infected computers or mobile devices. If you are not sure whether a message or email is legitimate or not, then check with your “friend” or check with the respective IT support team. Official correspondence usually come by mail or can also be accessed on the company’s website. Open the relevant page of the sender, e.g. the bank, manually in your browser.
If the email is not meant for you, then don’t let your curiosity get the better of you; delete the email promptly. Do not click on any link in the email or message and- again for emphasis- never open the attachment!
What can I do?
1. Be careful with suspicious emails and their attachments. Never provide any personal details in any website linked to in such messages.
2. If you are not sure whether you have perhaps already fallen prey to a phishing attack, then first check the computer for possible infections with our free removal tool (instructions in German). Change the login details from a clean computer.
3. Help fight cyber-criminals and report suspicious spam emails to the Internet Complaint Office.
How can I protect my computer?
1. Protect your computer from an infection by keeping your system up-to-date. Install anti-viral and security patches without delay. Be careful when opening unknown emails. Do not click on integrated links in such emails and never open their attachments.
2. Are you still working on a computer using the administrator rights? Reduce the administration rights to a minimum for everyday usage. Set up User Account Control for executable programs.
3. Back up your important files regularly and keep the backup separate from your computer. You should keep these handy in case your computer gets infected.
4. Use professional anti-virus software, also on a Mac.
5. Make sure that you have the most current version of your browser installed. You can check this and whether you are already part of a botnet here: botnet check.
Image: freedigitalphotos.net












